Introduction
As a SaaS-based lifecycle management solution for IT operations, OpsRamp is designed to ensure the confidentiality, integrity, and availability of critical data.
A standards-based security architecture is implemented to guarantee the highest levels of security, control, availability, and scalability.
Security is implemented at the following areas:
- agent
- gateway
- cloud
- operational controls
Agents and gateways
Agents are installed on customer target resources which are on a private network.
- The agent needs outgoing communication with the Gateway on 3128 (HTTPS proxy server).
- The agent establishes a connection with the connection grid in the Cloud after OAuth2-based authenticatiom.
Gateways are virtual appliances that collect data from the managed environment. Gateways have the following characteristics:
- Sit in a client internal environment with a private IP behind the firewall.
- Establish a secure connection to the Cloud over the internet via a secured tunnel that is based on TLS 1.2 with 256-bit encryption.
Agent properties
| Property | Description |
|---|---|
| Function | A lightweight agent that runs on Windows and Linux systems in the managed environment.
|
| Form factor | Windows and Linux binaries.
|
Gateway properties
| Property | Description |
|---|---|
| Access controls | All configuration updates for the Gateway are pushed from the OpsRamp Cloud using a 256-bit encrypted channel created by the Gateway. |
| Operating System | Hardened configuration of Ubuntu Server. Hardening includes the following measures:
|
| Form Factor | Gateway is a virtual appliance that runs on VMware vSphere and Citrix XenServer platforms. |
Connectivity requirements
The requirements for connectivity include:
| Property | Description |
|---|---|
| Outbound | Agents and gateways require outbound network connectivity to the cloud. If your organization has firewall policies to limit outbound access to specific IP addresses, then agents and gateways must have access OpsRamp IP addresses. |
| Inbound | N/A - OpsRamp does not impose any inbound connectivity requirements. |
Configuration options
The following diagram shows the following options:
- Each agent and gateway has a direct connection to the OpsRamp cloud.
- Each agent has a HTTP proxy connection to the gateway; Each gateway has a direct connection to the OpsRamp cloud.
- Each agent has a HTTP proxy connection deployed on a standalone server; Each gateway has a direct connection to the OpsRamp cloud.
Note
Agents work with any standard HTTP Proxy.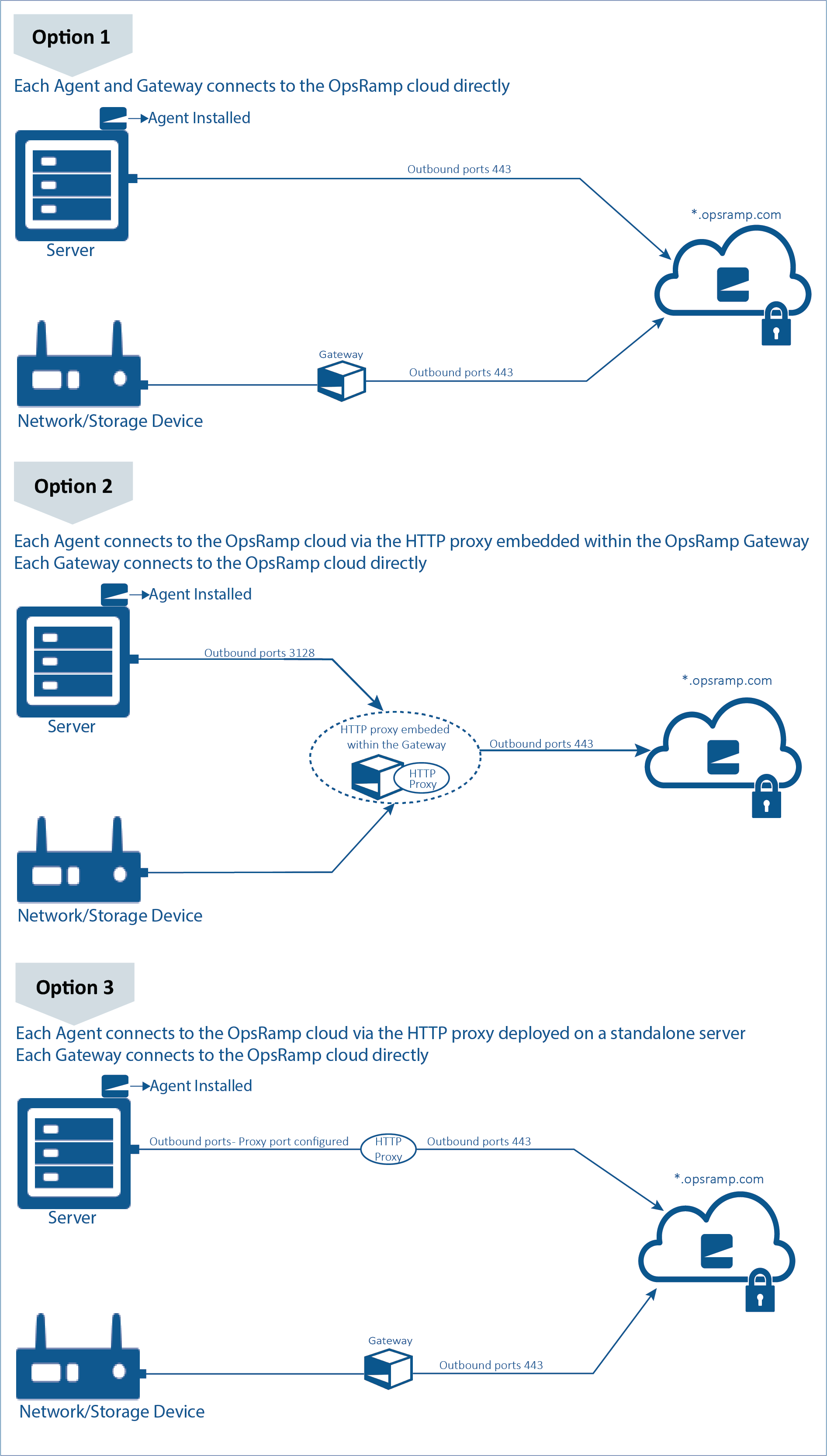
Connectivity Configuration Options
OpsRamp cloud
The OpsRamp application runs in data centers. It runs on company-owned physical hardware within co-location facilities in two (2) United States based data centers. These data centers do not run in a public cloud.
Data centers
The OpsRamp cloud is comprised of various components of the OpsRamp application, running on company-owned infrastructure. The two (2) data centers are owned and operated by two (2) different 3rd party data center providers. Both data center providers have publicly listed United States firms.
SAS70
OpsRamp data centers are certified with SAS70 Security Certification.| Location | Details |
|---|---|
| United States |
|
| Europe |
|
| Canada |
|
Data collection
OpsRamp collects and stores only data necessary to perform IT operations management functions on devices that it manages.
Data not collected
OpsRamp does not collect, and has no means to collect, any data processed by applications that OpsRamp monitors. Examples of such data include: data within database tables, the content of application transactions, user credentials of applications, etc.| Data Type | Data Collected | Data Storage and Security |
|---|---|---|
| Performance statistics | System-level information necessary to monitor the performance and health of managed devices:
| Device performance statistics are stored only in the cloud. The Agent and Gateway collect and transmit this data to the Cloud. |
| Events and SNMP traps | Operating System events and traps generated by SNMP agents. | The Gateway and Agent process events and traps locally and send resultant alerts to the Cloud via a secure channel. Raw event data is not stored in the Cloud. |
| Resource configuration and metadata | System-level information necessary to asset device configuration status:
| The Gateway and Agent send configuration data to the Cloud via a secure channel |
| Device Credentials | Credentials (username/password) necessary to discover devices, access performance, and configuration data, and log into devices to run automation scripts. | The IT administrator provides device credentials to OpsRamp via its user interface. Device credentials are stored in the Cloud, using industry standard 2048-bit RSA encryption. |
Data management
| Property | Description |
|---|---|
| Data classification | OpsRamp only collects and stores data required for IT operations management on devices and applications managed by it. Data that OpsRamp collects is limited to device performance metrics, performance and failure events, and configuration information. |
| Data isolation | OpsRamp implements strict multi-tenancy controls to ensure data access is strictly isolated between customers. |
| Data encryption (in-flight) | All data transmitted between the Agent/Gateway and the Cloud is encrypted with TLS v1.2 standards. |
| Data encryption (at-rest) | Resource credentials stored in the Cloud is encrypted using 2048-bit RSA encryption. |
| Authentication | Cloud offers SAML and OAuth2 based authentication. OpsRamp additionally supports third-party authentication services such as OneLogin, Okta, and ADFS. Cloud offers two-factor authentication. |
| User access management | OpsRamp has extensive role-based access controls. OpsRamp access controls are granular to the managed device, user, and feature. | APIs | OpsRamp provides REST APIs for integration with cloud. OpsRamp REST APIs are backed by OAuth2 based authentication. | Regulatory and Compliance Requirements | OpsRamp does NOT collect any Personally identifiable information (PII). OpsRamp is hosted in co-location facilities provided by two United States based data center providers. Each provider has their own security certifications including SAS and SSAE. |
Data security
OpsRamp supports an extensive set of security features to ensure that management data collected by OpsRamp is accessed only by authorized users.
| Property | Description |
|---|---|
| Encryption | All sensitive data is encrypted in OpsRamp. Customer data (inventory, metrics, alerts, and tickets) is logically partitioned and stored under-tenant. Customer data is accessible only to authorized users of the tenant. |
| Role-based access control | OpsRamp supports comprehensive role-based access controls. Users’ access to devices and actions within OpsRamp is controlled by fine-grained permissions. Permissions are assigned based on users’ roles. |
| Identity management | OpsRamp provides multiple options to manage user identity:
|
| Authentication | OpsRamp supports two-factor authentication using Yubico YubiKey. |
| Passwords | OpsRamp follows standard practices for passwords:
|
Data retention
On contract expiry, OpsRamp inactivates the tenant in the OpsRamp platform. An inactive tenant’s instance inventory, metrics, and alerts data is available in the passive state in the platform. However monitoring, alerting and another management functionality is no longer available.
Based on a mutual agreement between OpsRamp and the customer, OpsRamp will delete all the tenant information from the Cloud. Due to a ninety-day data archival retention policy, deleted tenant data will be available in the archival repository for ninety days. for more information.
Application access
Role-based access controls support fine-grained access control based on user and user groups, device and device groups, specific features, and resource credentials.
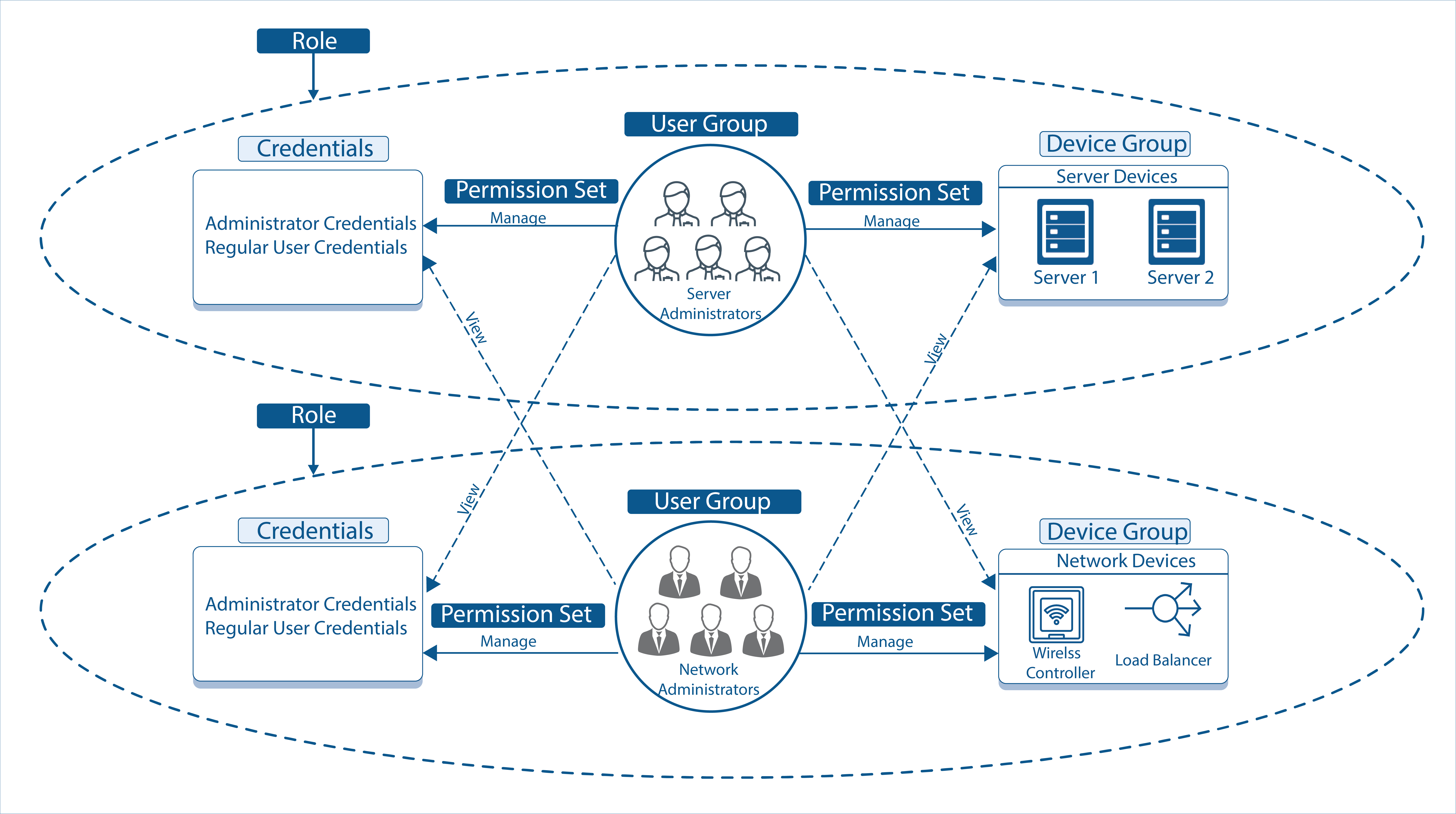
Role-based Access Control
Operational controls
Operations and development processes follow methodologies that ensure the security of managed data.
SOC 2 Type II
OpsRamp is SOC 2 Type II certified.| Property | Description |
|---|---|
| Infrastructure management | The infrastructure on which OpsRamp runs is managed to industry standard practices:
|
| Audit processes | Customers can run their own security audit on the Agent, Gateway and publicly facing OpsRamp URLs. The Cloud is managed using another instance of OpsRamp and audit recordings of management activities on OpsRamp can be provided as needed. |
Infrastructure operations
OpsRamp is hosted in a private network. All the infrastructure elements (ESX/XEN hosts and network elements) run in the management network which is accessible only by VPN. A dedicated instance of the OpsRamp platform is used to manage SaaS infrastructure operations. Resources are isolated under multiple network layers to minimize risk. Any access to the infrastructure will be captured through audit recordings in OpsRamp. All changes to infrastructure are governed by a Change Advisory Board (CAB) as per ITIL standards.
Production access controls
Physical access to the production area is controlled by biometric and smart card access. Access to data centers is restricted to authorized personnel with 24×7 security monitoring and CCTV surveillance across the facilities.
Intrusion prevention
OpsRamp production environments are protected by 24×7 automated network level intrusion prevention systems. IP and port-based firewalls continuously monitor authentication logs on Linux servers. Inbound and outbound traffic at various entry points is monitored and vulnerability checks are performed on servers regularly. In case of any breach, additional firewall rules are used to block the specific IP ranges. Linux, database passwords, encryption keys, and algorithms are changed. Customers are required to change passwords and take additional measures for ensuring security.
Risk and mitigation
| Potential Compromise | Risk | Mitigation |
|---|---|---|
| Master database |
|
|
| Big data layer |
| |
| File system | Encrypted recordings get exposed. |
|
| Codebase | Encryption management Algorithms |
|
Disaster response
OpsRamp SaaS platform is hosted in co-location facilities provided by two United States based data center providers in San Jose, CA and Rancho Cordova, CA. Real-time two-way data replication is enabled between the two data centers. Processes are in place to verify 24×7 cross data center replication. In the case of primary data center outage, DNS routing change is performed to make the secondary data center as primary.